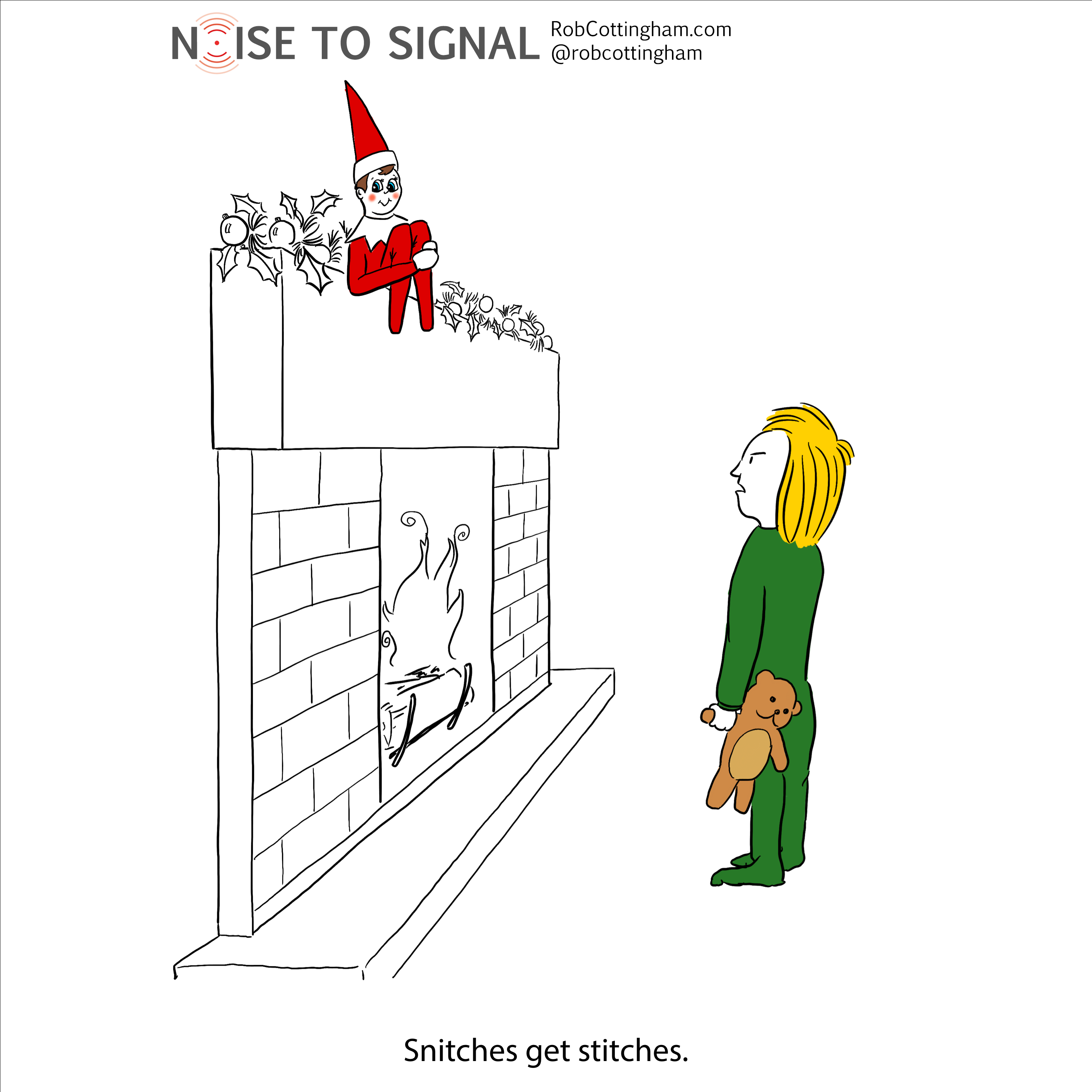
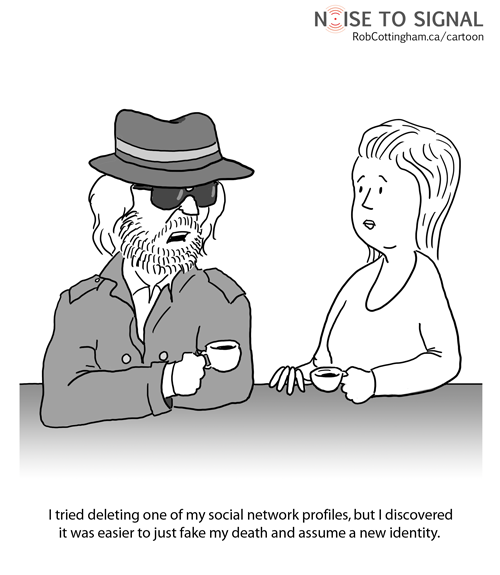
Guys: just don’t, okay?
* * *
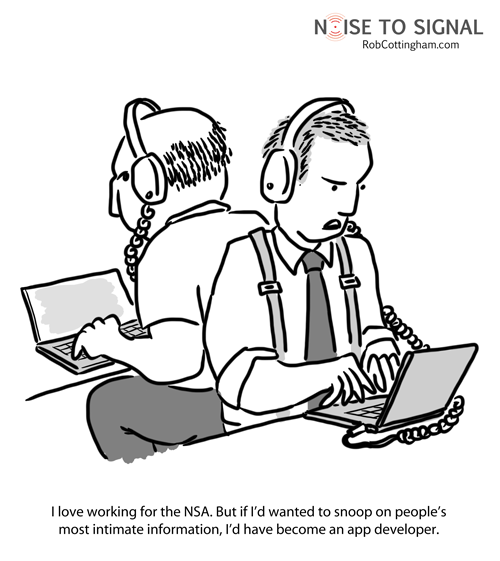
I have a pair of big ear-can headphones: the Sony MDR-7506, acquired used on Craigslist last year. I haven’t used headphones this big since… wow, since high school.
It seemed like overnight everyone stopped using them in the 80s, and started sporting tiny foam Sony Walkman headphones. Its headband looked so tiny and fragile that I couldn’t believe it would survive the rough and tumble of my backpack on a daily commute to and from university. And yet…
…well, actually, it broke pretty quickly, as did its replacement. But soon the market responded with cheap knock-offs with sound every bit as good as Sony’s.
A few years later, along came earbuds, which became the must-have audio accessory once the iPod debuted. Wonderful for most people, but hellish for me because I couldn’t figure out how to use them properly. They kept falling out, and I started to feel increasingly stupid at not being able to grasp this simple technology.
Then David Pogue saved me with a column revealing I wasn’t alone. He and I and lots of other people lack a little nub of ear cartilage known as the antitragus which, for most of the world, holds those earbuds in snugly.
It took me a few years after that to finally shell out for the big ol’ headphones of my youth, but I did and I’m happy. The kids are finally at an age where me isolating myself with a little music isn’t going to threaten anyone’s safety. And they’ve grown up on much smaller headphones, so neither one is pestering me to use these.
Truth be told, they’re heavy and inconvenient, and I actually prefer to wear a lightweight pair of cheap off-brand Bluetooth headphones for day-to-day use. But when I want to disappear into a cocoon of sound, there’s nothing like two 1970s-style ear-mattresses to do the trick.