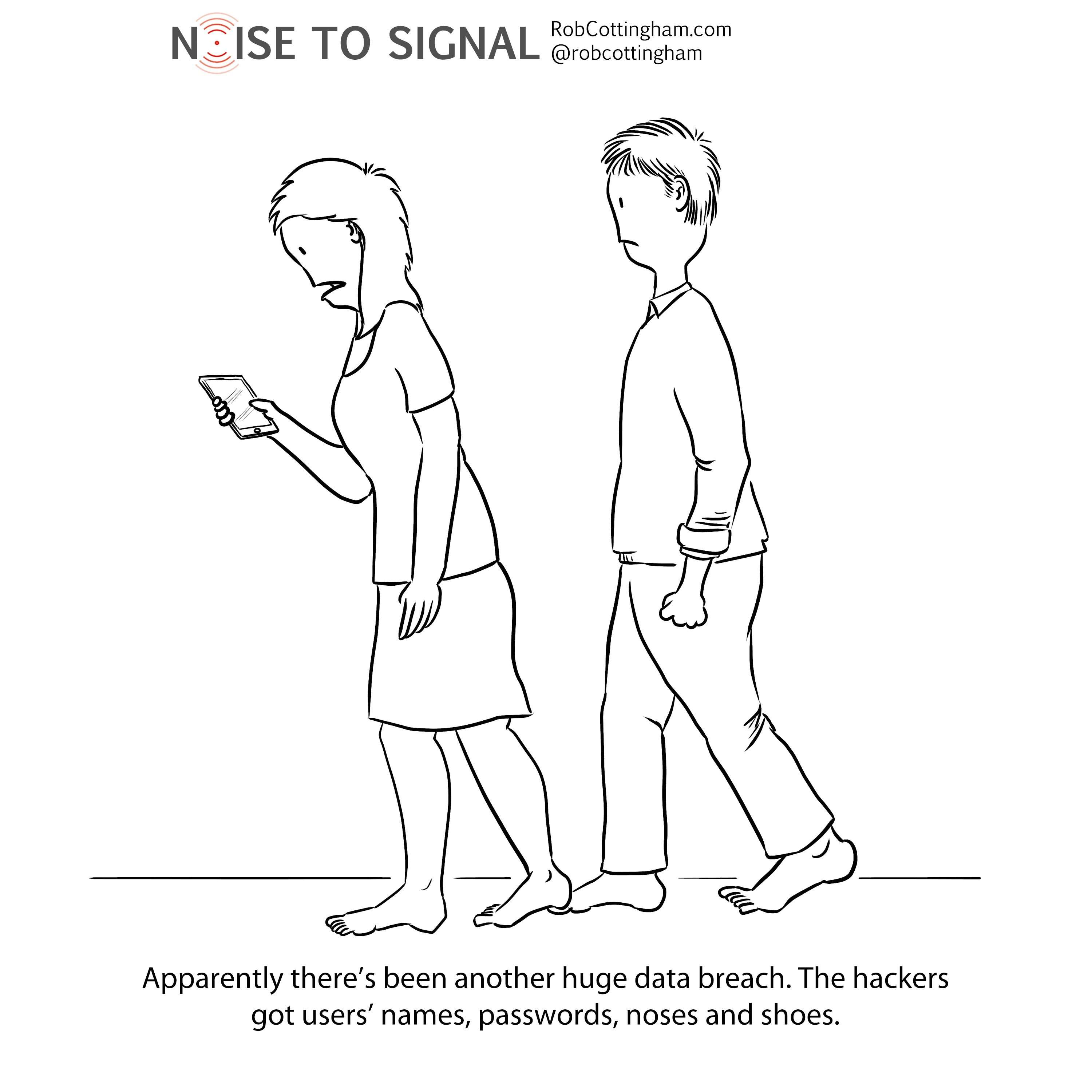
Another day, another data breach —this time with a British teleco called TalkTalk. Unlike the Ashley Madison breach, the very fact that someone’s profile is in their database isn’t damaging, but the personal information attached to that profile could be.
There’s a ton of good common-sense security advice out there for users (the folks we used to call “consumers”). Use a different password on every site. Use hard-to-guess passwords. Be careful of public Wi-Fi. Don’t have children.
That’s fine for locking up our own front doors. But how to protect ourselves when someone breaks into the bank vault and raids our safe deposit boxes? In terms of defending ourselves from third-party security breaches, there isn’t a lot of advice out there — other than “don’t share any more information than you have to.”
Unfortunately, many of the companies we deal with make sharing more data than necessary part of the price of doing business with them. And that’s not just the data they gather in a registration form; they track how we use their services relentlessly, and cross-reference that data with information from other services.
Everything they have on us is there on their servers, ready for an enterprising hacker to swoop in and harvest if the company fails to mount an adequate defence. There isn’t a lot you can do about that; we don’t even have a good sense of how well the companies we deal with are protecting our data, because they’re notoriously tight-lipped about their security practices, citing security concerns.
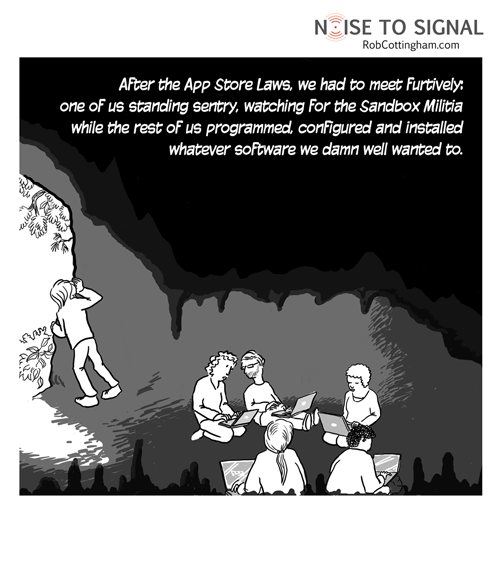
The key message is just “Trust us,” which doesn’t inspire confidence with the mounting pile of headlines suggesting many data warehouses aren’t impregnable fortresses so much as all-you-can-download buffets. That’s especially frustrating if you’re otherwise careful about protecting your privacy. It doesn’t do you a lot of good to cover your tracks if your partner in crime (or data) sings like a canary.
Worse yet, you don’t have to be a customer to run afoul of a company’s disregard for your privacy and security. In their quest for ever-harder-to-ignore ads, companies have embraced Flash-based tools that expose browsers to gaping security holes.
Which is why the breaches we’ve seen so far are probably just prologue. As Cory Doctorow put it, “Ashley Madison and the Office of Personnel Management weren’t the big leak-quake: they were the tremors that warned of the coming tsunami. Every day, every week, every month, there will be a mounting drumbeat of privacy disasters. By this time next year, it’s very likely that someone you know will have suffered real, catastrophic harm due to privacy breaches. Maybe it’ll be you.”